Intrusion Prevention Systems (IPS) provides enterprises and service providers with unparalleled protection against external and internal attacks. Exponential rises in the number of application vulnerabilities and increasingly complex gigabit-level DOS (Denial of Service) attacks have rendered traditional Firewalls ineffective at protecting today’s networks. While Intrusion Detection Systems (IDS) can often detect these attacks, these passive systems offer little more than an after-the-fact notification.
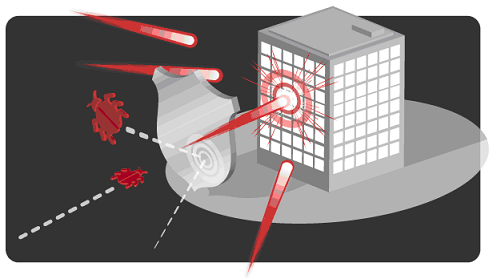
Intrusion Prevention System (IPS) solutions are designed to examine all traffic that passes through it to detect and stop undesired access, malicious content and inappropriate transaction rates from penetrating or adversely affecting the availability of critical IT resources. Analogous to anti-virus systems, IPS units can be centrally managed and armed with additional filters whenever a new vulnerability is discovered. More akin to switches than sensors, IPS units are typically installed as part of the network infrastructure, both at the perimeter and in the core of the network.
IPS are primarily focused on identifying possible incidents. For example, an IPS could detect when an attacker has successfully compromised a system by exploiting a vulnerability in the system. The IPS could then report the incident to security administrators, who could quickly initiate incident response actions to minimize the damage caused by the incident. The IPS could also log information that could be used by the incident handlers. Many IPS can also be configured to recognize violations of security policies. For example, some IPS can be configured with firewall ruleset-like settings, allowing them to identify network traffic that violates the organization’s security or acceptable use policies. Also, some IPS can monitor file transfers and identify ones that might be suspicious, such as copying a large database onto a user’s laptop.
Many IPS can also identify reconnaissance activity, which may indicate that an attack is imminent. For example, some attack tools and forms of malware, particularly worms, perform reconnaissance activities such as host and port scans to identify targets for subsequent attacks. An IPS might be able to block reconnaissance and notify security administrators, who can take actions if needed to alter other security controls to prevent related incidents. Because reconnaissance activity is so frequent on the Internet, reconnaissance detection is often performed primarily on protected internal networks.
In addition to identifying incidents and supporting incident response efforts, organizations have found other uses for IPS, including the following:
- Identifying security policy problems. An IPS can provide some degree of quality control for security policy implementation, such as duplicating firewall rulesets and alerting when it sees network traffic that should have been blocked by the firewall but was not because of a firewall configuration error.
- Documenting the existing threat to an organization. IPS log information about the threats that they detect. Understanding the frequency and characteristics of attacks against an organization’s computing resources is helpful in identifying the appropriate security measures for protecting the resources. The information can also be used to educate management about the threats that the organization faces.
- Deterring individuals from violating security policies. If individuals are aware that their actions are being monitored by IPS technologies for security policy violations, they may be less likely to commit such violations because of the risk of detection.
There are four different types of intrusion prevention systems :
- Network-based Intrusion Prevention (NIPS): monitors the entire network for suspicious traffic by analyzing protocol activity.
- Wireless Intrusion Prevention Systems (WIPS): monitors a wireless network for suspicious traffic by analyzing wireless networking protocols.
- Network Behavior Analysis (NBA): examines network traffic to define threats that bring about unusual traffic flows, such as distributed denial of service (DDoS) attacks, certain forms of malware, and policy violations.
- Host-based Intrusion Prevention (HIPS): an installed software package which monitors a single host for suspicious activity by analyzing events within that host
Because of the increasing dependence on information systems and the prevalence and potential impact of intrusions against those systems, IPS have become a necessary addition to the security infrastructure of nearly every organization.