You can't stop what you can't find. That's why you need network forensics. Active network forensics makes all network data flows instantly visible and replayable, enabling administrators to detect the full source and scope of any network security event and protect the network against further attack. Combining high-speed data capture, indexed storage, and comprehensive analysis tools, active network forensics is analogous to putting a security camera on your network. Doing so instantly exposes any specific network event, making even the most sophisticated and targeted network attacks plainly visible.
Network forensics fills an important gap in today’s network security landscape by capturing, indexing and replaying all data and providing full context and actionable evidence to stop a security incident. Network forensics solutions improve the effectiveness of network security technologies such as Firewalls, IPS, DLP, SIEM and Log Management tools by recording all network traffic at full line rate.

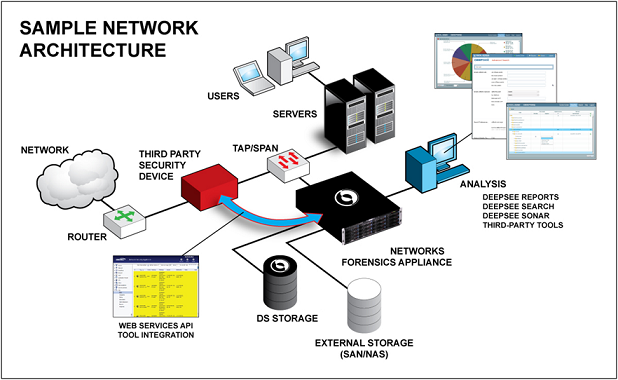
The network forensic appliance deploys anywhere on your network: at the perimeter or the core; 10 Gb backbones, remote links, or even within virtual hosts, enabling you to record and analyze everything and protect against targeted, persistent threats. The appliances integrate capture, indexing, and analysis into a single platform, eliminating the need for complex multi-box solutions.
The network forensics appliances provides visibility into all of the data that crosses an enterprise’s network. The series includes the only available network forensics appliance that can sustain full total packet capture, recording and indexing at the speeds of today’s fastest enterprise networks, including 10Gb networks.
Network forensics appliances can be deployed as dedicated hardware appliances or virtual appliances. They can even be deployed inside a virtual network comprised of intercommunicating virtual machines, enabling them to expose their virtual traffic to external physical security tools for analysis. Regardless of the deployed method, the solution sit passively on the network via an available SPAN port on a switch or a network tap device such that it doesn’t interfere with network traffic, remaining essentially invisible and non-detectable from the targeted network segment.
The special purpose of packet capture file system in the network forensic appliances is designed specifically to allow the appliances to automatically capture and store all the data packets that flow across the network, even up to speeds of 10Gbps and storage partitions up to one petabyte in a single location. As storage capacities expand in the future, the network forensic appliances can scale to support those higher capacities.
At its most basic level, the solution takes network data packets from a network interface card (NIC), classifies the network flows, and then moves that data to storage in a specialized format that has been optimized for extremely high throughput storage, accuracy, manageability, and security. In addition to enabling organizations to capture 100% of network traffic, the network forensic appliances also provide complete control over the type of traffic captured. It provides the option to filter network traffic, either during capture or when replaying captured traffic at a later time.
The appliances classify every network flow by looking deep within the packet data to find and match the unique fingerprint of the actual application. It categorizes applications into 28 different families and identifies over 490 applications and protocols. In addition, its ability to extract details like email addresses, URLs, instant messaging usernames, search engine queries, or social network personas allows it to develop a vivid description of network flows. This vivid and accurate classification provides the real situational awareness required to defend against next generation threats as well as improves the time to remediate with active response.
As an appliance captures and stores each packet, its internal database creates an entry for that packet that includes key identifying attributes relating to the packets and the sessions that the collection of packets make up. These attributes include network-layer attributes such as sending and receiving IP addresses, MAC addresses, and ports. It also includes application-layer attributes such as application name and family, user identities, requested actions, and content.